Securing AI in the Defense Industrial Base: Old Principles, New Urgency
The most dangerous moment in any technology transition is when the excitement of the new causes organizations to forget what they already know. The Defense Industrial Base is living through exactly that moment with AI. And yet the fundamentals of securing these systems have not changed. We are not inventing new security principles here. We are applying proven ones to a more consequential environment.
Consider the stakes. DIB contractors operate under CMMC, ITAR, and a growing web of regulatory frameworks designed to protect Controlled Unclassified Information and, in many cases, classified data adjacent to program-sensitive work. AI systems introduced into these environments are not just productivity tools. They are data processors, decision influencers, and in some configurations, autonomous actors operating at machine speed across networks that were never designed with that assumption in mind. That changes the threat surface. It does not change the answer.
Three principles matter more now than they ever have.
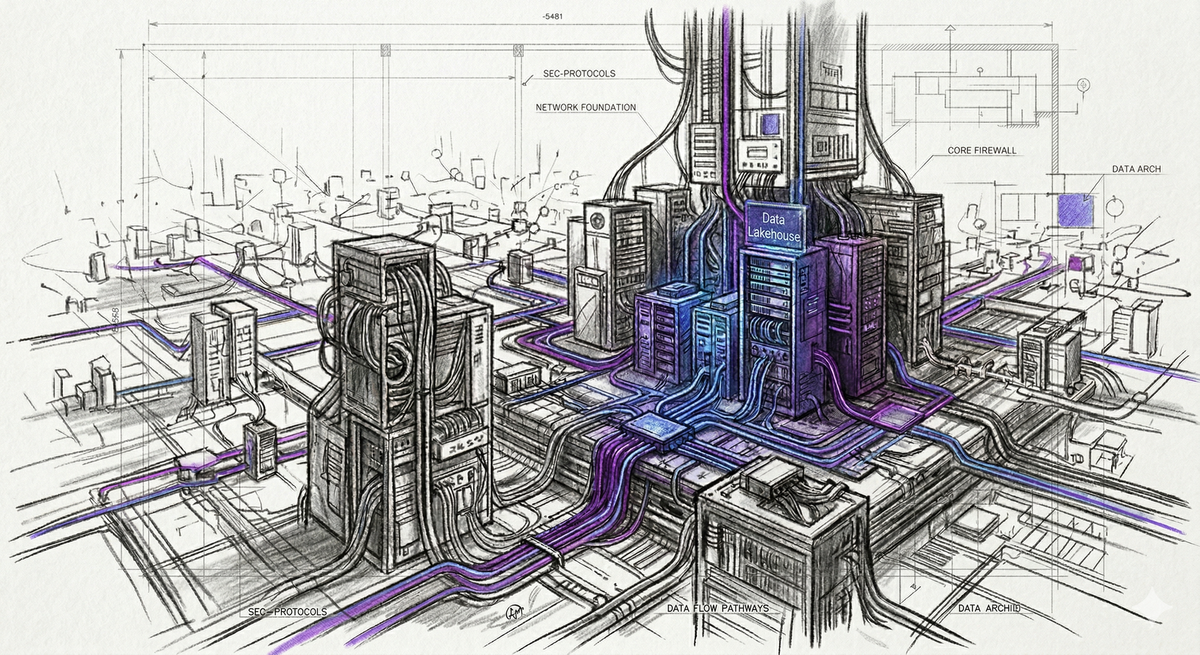
The first is following the data. AI systems are, at their core, data transformation engines. Training data, inference inputs, retrieval-augmented content, and model outputs all represent potential exposure points. In a DIB context, a single misconfigured pipeline can inadvertently ingest CUI, exfiltrate it through a model API, or expose it to a third-party service never cleared for that information. The question is not whether your AI tool is impressive. The question is whether you can trace every byte it touches, from origin to output, with the same rigor your compliance team applies to a data flow diagram in a System Security Plan.
The second principle is observability. If you cannot see what your system is doing, you cannot defend it. This has always been true. AI makes it harder and more important simultaneously. Model behavior is not always predictable, and prompt injection, data poisoning, and model inversion attacks are not theoretical in adversarial environments. For organizations supporting DoD programs, the adversary is not abstract. Logging inference activity, monitoring for anomalous query patterns, and maintaining audit trails of AI-assisted decisions are not optional layers. They are the difference between detecting a compromise and reading about it in an incident report six months later.
The third principle is identity and permissions. The principle of least privilege did not become less important because the entity requesting access is now a service principal rather than a human. AI agents, orchestration frameworks, and automated pipelines all need identities, and those identities need to be governed with the same rigor applied to privileged human accounts. In practice, this means integrating AI workloads into your existing Privileged Identity Management and Privileged Access Management frameworks rather than treating them as exceptions. In other words, the identity of each agent needs to be a first class identity. It means ensuring that the model calling your API has only the permissions it needs, that those permissions are time-bound where possible, and that every access event is logged and reviewable.
None of this is exotic. It is the same discipline that mature security programs apply to cloud infrastructure, endpoint management, and network segmentation. The organizations that will navigate the AI transition successfully in the DIB are not the ones chasing the most capable model. They are the ones that treat AI as infrastructure, govern it accordingly, and resist the temptation to let capability outrun accountability.
The hype will pass. The regulatory scrutiny will not. Build the foundation now.
🤖 AIL LEVELS: This content’s AI Influence Levels are AIL2 for the writing, and AIL4 for the images. AI Influence Level (AIL) framework